Documentation Index
Fetch the complete documentation index at: https://academy.pathfindr.ai/llms.txt
Use this file to discover all available pages before exploring further.
- Verify domains → enable SSO → optionally enable automatic account creation → connect SCIM.
- Keep RBAC simple with 3–4 groups mapped to lightweight custom roles.
- Default sharing to invite-only or workspace-only; allowlist Actions domains before enabling.
- Leave connectors off by default and grant per role or group.
- Finalize retention, residency, and IP allowlists before pilots sign in.
- Automate Compliance API exports to your eDiscovery or SIEM tooling.
Secure workspace access
Configure AI policy reminders
Design roles & guardrails
Govern GPT publishing
Automate compliance & discovery
Launch & onboard teams
Secure workspace access
Confirm identity, provisioning, and baseline workspace policies before inviting a broad audience.Verify corporate domains
Enable SAML SSO
(Optional) Automatic account creation
Provision with SCIM
Harden workspace policies
- Add TXT records and verify all corporate domains.
- Turn on SAML SSO and test with a 3–5 person pilot group.
- Decide whether automatic account creation is in scope for phase one.
- Connect SCIM and sync pilot groups first.
- Lock IP allowlists, retention, and data residency before rollout.
- Configure the AI policy modal to remind users of organizational policies.
Configure AI policy reminders
Keep your organization’s AI policies visible with the Enterprise AI Policy Modal.Enterprise AI Policy Modal
From Workspace Settings → General, admins and owners can customize a modal that reminds users of your organization’s AI policies. In the Workspace Policy section, you can define specifics of your organization’s AI policy.Navigate to workspace settings
Define your AI policy
- Keep the policy concise and actionable—users should understand key rules at a glance.
- Reference your full Acceptable Use Policy for detailed guidance.
- Update the modal when policies change to trigger an immediate reminder to all users.
- Coordinate with your legal and compliance teams to ensure the policy text aligns with organizational standards.
Design roles and guardrails
Keep permissions predictable without slowing pilots.Roles
Groups
| Group | Role(s) assigned | Connectors enabled |
|---|---|---|
| All employees | Default employee | none |
| Builders | Builder | none (sandbox only) |
| Engineering & data | Default + connector user | GitHub, Drive, SharePoint (allowlisted) |
| Finance & HR | Default (no connectors) | none |
| Legal & compliance | Default | internal tooling only |
| Frontline & field | Default (reduced) | none |
| Contractors | Default (reduced) | none |
- Create high-level groups and assign pilot members.
- Build custom roles with only the required toggles.
- Assign roles to groups (not individuals) and test with a sample user.
- Keep sensitive connectors fenced to specific groups.
- Schedule a quarterly RBAC and connector review.
Govern GPT publishing
Default to safe sharing, then widen scope as governance and review processes mature.- Actions domains
- Connectors
Recommended publish flow
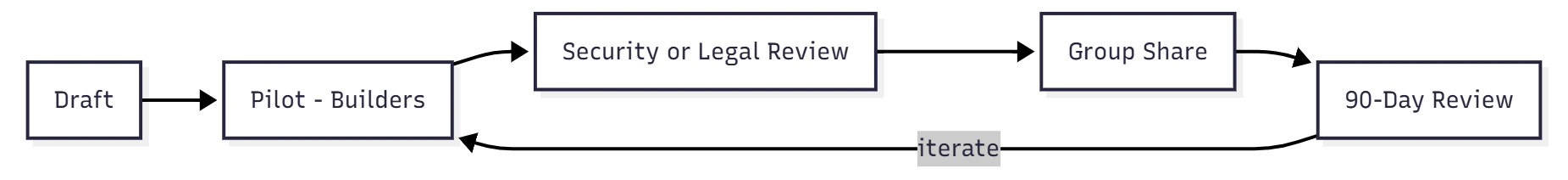
- Set default sharing to invite-only or workspace-only.
- Create and maintain an Actions domain allowlist.
- Gate each connector behind a business case plus RBAC scope.
- Require review for GPTs that touch regulated or customer data.
- Schedule a 90-day lifecycle review to archive unused GPTs.
Automate compliance and discovery
Turn on audit-grade logging, plan discovery workflows, and keep regulated content traceable.Compliance API exports
Export conversation metadata, GPT events, and Records for eDiscovery, DLP, or SIEM. Compliance endpoints respect IP allowlists—configure IP restrictions before issuing API keys. Use User Analytics for adoption trends and reserve the Compliance API for audit logging.- Issue a Compliance API key to your security or legal owner.
- Apply IP allowlists to the compliance endpoints.
- Automate daily exports to your SIEM or data lake.
Integrate Microsoft Purview
Pick your ingestion route
Configure ingestion
Launch and onboard teams
Deliver a great first-run experience while enforcing endpoint controls and change management.Enforce endpoint DLP for browsers
Deploy the Purview extension for Chrome on Windows. macOS enforcement does not require the extension. Roll out only after devices are onboarded to Endpoint DLP so policies take effect immediately.Admin playbook
Pilot with admins, security, and builders before broad access. Track adoption in User Analytics (export CSVs for deeper reviews) and share guardrails plus department-specific starter prompts ahead of go-live.Individual setup
Sign in with SSO
Sign in with SSO
Set Custom Instructions
Set Custom Instructions
Join the right groups
Join the right groups
Use internal GPTs first
Use internal GPTs first
Handle files and data carefully
Handle files and data carefully
- Pilot with builders and security, and publish a small internal GPT library.
- Share “Start here” guidance plus role-specific prompt packs.
- Monitor weekly adoption and coach low-usage teams.
- Review RBAC, connectors, and GPT inventory quarterly.
Appendix
Roles and capabilities
Roles and capabilities
RBAC design
RBAC design
Group-level sharing
Group-level sharing
Identity & provisioning
Identity & provisioning
Connector administration
Connector administration
Compliance API logging
Compliance API logging
User Analytics dashboards
User Analytics dashboards
Data retention & residency
Data retention & residency
IP allowlisting
IP allowlisting
Microsoft Purview controls
Microsoft Purview controls
Self-check: First-time admin test
- I can see the five focus areas above the fold and know where to start.
- Each section begins with Steps/Tabs and ends with a quick checklist I can tick through.
- I know the safe defaults (SSO on, connectors off, invite-only sharing, domain allowlist for Actions).
- I have a clear path to auditability (Compliance API + Purview) and a 90-day review loop.